In this article, I explore the recent joint advisory by the NSA and CISA, highlighting the top 10 cybersecurity misconfigurations commonly found in large organizations’ networks.
Introduction
My reflections in this post are based on the findings I’ve read in the NSA/CISA report. The report contains all the details, including reasoning and mitigations. My reflections are on a higher altitude and talks to decision makers – remember, security is a shared responsibility.
Why do you need to know about this report?
Teams must shift left, adopt a proper Secure Development Lifecycle (SDLC or SDL), and ensure everyone moves the needle toward the shared responsibility of security in their organizations.
- The report highlights some of the most common network misconfigurations seen in the wild and contains a load of advice for mitigation.
You’ve probably seen some or all misconfigurations before. However, it’s now a tangible list.
How is this different from OWASP Top 10?
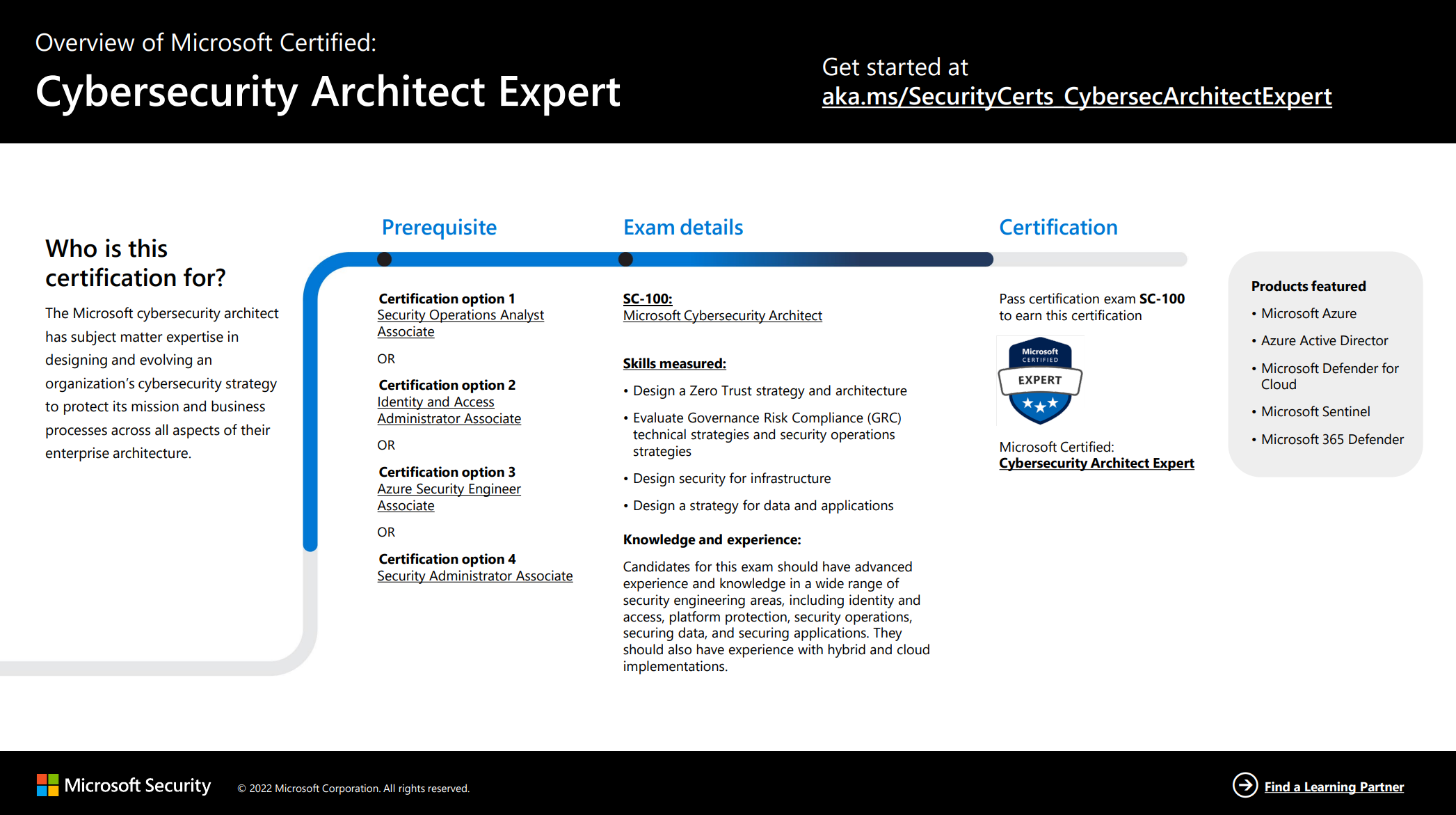
Both the security misconfiguration report by NSA and CISA and the OWASP Top 10 talk about security misconfigurations or vulnerabilities. However, the focus areas are different.
The OWASP Top 10 list focuses more on web application vulnerabilities, while the NSA/CISA advisory addresses broader network and system misconfigurations.
Security assessments run on familiar environments
The report also highlights what environments they ran their assessments on:
“Many of the assessments were of Microsoft Windows and Active Directory environments.”
- https://www.cisa.gov/news-events/cybersecurity-advisories/aa23-278a
The same rules and practices apply if you’re working with Microsoft technologies or something else. You’ll benefit from understanding these common misconfigurations and how to mitigate them.
Delve into my reflections below. I’m scoping this post to the business- and IT leaders, not implementers – the report already contains much of that.
Top 10 cybersecurity misconfigurations
Here are the common misconfigurations in networks for large organizations, followed by my reflections for IT leaders.
1. Default configurations of software and applications
Many software applications and systems have default configurations to ease the setup process. These configurations, however, are often insecure, creating potential avenues for unauthorized access. Attackers are well-versed with these default settings and can exploit them to infiltrate networks, gain unauthorized access, and potentially cause significant damage.
Strategic mitigation
Adopt a policy where software is deployed with the most secure settings by default.
- For example, consider adopting the secure-by-default policy in your organization and teams to ensure the most secure settings are configured, always, and by default.
2. Improper separation of user/administrator privilege
This misconfiguration occurs when users have more access rights than necessary or administrative privileges are too loosely assigned. It may lead to unauthorized access to sensitive areas of the network or system and potential misuse either accidentally or maliciously.
Strategic mitigation
Implement robust access control policies in your organization, ensuring users have the least privilege necessary to perform their tasks.
- For example, adopt the Zero Trust principles, including least-privilege access.
3. Insufficient internal network monitoring
Malicious activities or system misconfigurations may go unnoticed without proper internal network monitoring until it’s too late. This lack of visibility can delay the detection of security incidents, making mitigation more challenging and potentially more damaging.
The longer a security incident goes undetected, the more severe the consequences can be, including, for example, extensive data loss, legal liabilities, and reputational damage.
Strategic mitigation
Establish a comprehensive security monitoring strategy to ensure timely detection and response to security incidents.
Relevant reading:
- NCSC Cyber Assessment Framework - Security monitoring (NCSC.gov.uk)
- Continuous security monitoring strategy - 5 key components (Bitsight)
- Security monitoring with the Azure Well-Architected Framework (Microsoft)
- Security management and monitoring (Microsoft)
- Microsoft Cloud Adoption Framework - Monitor and protect at cloud-scale (Microsoft)
4. Lack of network segmentation
Network segmentation divides a network into smaller parts to control traffic and enhance security. Without segmentation, malicious actors can move laterally across the network once they gain access, which leads to widespread system compromises, data breaches, and the potential for increased disruption and financial loss, as a few examples.
Strategic mitigation
Adopt network segmentation to control traffic and reduce the attack surface. Ensure this is standard practice across your cloud environments and that all teams, including development, infrastructure, central IT, and any Cloud Center of Excellence teams, know the segmentation requirements.
- Implement network segmentation patterns on Azure (Microsoft)
- CISA Layering network security through segmentation (CISA)
5. Poor patch management
Failing to apply patches promptly leaves systems vulnerable to known vulnerabilities that attackers can exploit. Poor patch management practices, like not prioritizing patches for critical vulnerabilities or not patching systems promptly, can lead to security incidents, data breaches, and compliance violations, which can be costly and damaging to the organization’s reputation.
Strategic mitigation
Develop a robust patch management process to ensure timely updates.
- Consider the complexities of pathing live environments, and the Patch dilemma, and make sure you have the buy-in to fix this in your organization!
- More specifically, you can invest in Azure Update Manager and Azure Automation Update Management capabilities for some Azure-relevant patch management.
6. Bypass of system access controls
System access controls are meant to ensure that only authorized individuals can access certain information. If these controls can be bypassed, unauthorized users could access sensitive data or systems, leading to potential data leaks, data corruption, and other serious security issues, which can have severe financial and reputational consequences.
Strategic mitigation
Strengthen access controls and regularly audit them for effectiveness.
- What is access control?
- Defining access control, types of access control, how it works, what the value is, and how to successfully implement proper access control.
- Access control
- Evaluate the access control considerations in the Microsoft Cloud Adoption Framework for Azure.
7. Weak or misconfigured multifactor authentication (MFA) methods
Multifactor authentication (MFA) is a crucial security measure. Still, when it’s weak or misconfigured, it can be easily bypassed, giving attackers unauthorized access to systems and data, leading to data breaches, financial loss, and damage to the organization’s reputation.
MFA misconfigurations can include weak authentication methods or incorrect configurations that don’t adhere to best practices.
Remember,
MFA can block over 99.9 percent of account compromise attacks
It’s one of the most critical flaws in your infrastructure if you haven’t configured, or incorrectly configured, MFA.
Strategic mitigation
Don’t ever compromise on this. Get organizational support all the way to implement strong MFA methods and ensure they are correctly configured. You can’t follow a Zero Trust approach and have a strong security posture in your organization if you don’t enforce MFA.
- Multifactor authentication in Microsoft Entra (formerly Azure AD)
- Multifactor authentication for Microsoft 365
8. Insufficient access control lists (ACLs) on network shares and services
Insufficient ACLs can allow unauthorized access to network shares and services, for example. This can lead to unauthorized data access, data corruption, data loss, data breaches, legal liabilities, and significant financial and reputational damage.
Strategic mitigation
Review and strengthen ACLs to ensure only authorized access to network resources like shares and services. You may have to audit all your resources for their access control list configurations.
9. Poor credential hygiene
Poor credential hygiene includes sharing credentials, using weak passwords, and not rotating passwords regularly. These practices can lead to unauthorized access and misuse of systems and data.
This is important not just for your users’ passwords and secrets but all credentials you manage one way or the other. Ensuring your systems can rotate keys, secrets, and certificates is equally important.
Strategic mitigation
- Enforce strong password policies and educate employees on maintaining good credential hygiene.
- Ensure you have policies in place for key, secret, and certification rotation.
- Don’t ever let weak credentials into the mix, whether on the user or the systems side.
10. Unrestricted code execution
Unrestricted code execution allows attackers to execute malicious code within the network. If not properly mitigated, this can lead to data breaches, system disruptions, system damage, complete system takeovers, and can lead to legal liabilities, loss of customer trust, brand damage, and more.
Strategic mitigation
Ensure your organizational security posture includes policies to enforce restrictions on code execution to allow trusted sources only.
Strategically improve your cybersecurity
In the previous section, we learned about the top 10 cybersecurity misconfigurations the NSA and CISA found and some of my reflections on the potential impact. In their report, mitigations exist for network defenders and implementers.
To explore popular cybersecurity frameworks and learn how to build a better security culture and to increase your security posture, read this next:
Closing thoughts and links
As we see with the report, there are plenty of common cybersecurity misconfigurations we can encounter in the wild - so if you’re a leader in your organization, now is a great time to make sure you’ve got the security alignment figured out across the company.
Hopefully you’ll find some relevant resources in the guidance linked here, and some thoughts on why it matters.
Here’s the reports, linked from both CISA and NSA.
 Tobias Zimmergren on TechTobias Zimmergren
Tobias Zimmergren on TechTobias Zimmergren
Comments are closed