Log Analytics
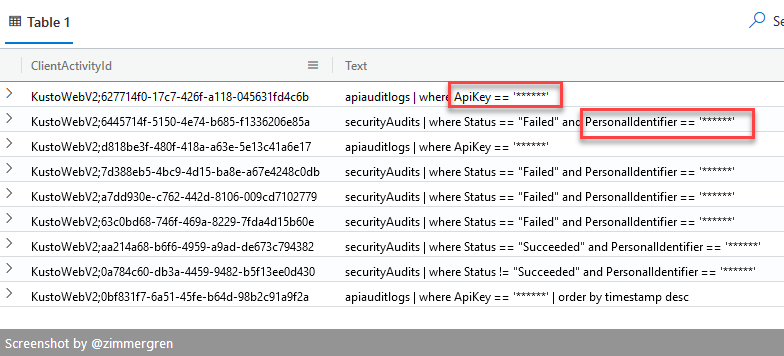
Obfuscate strings in KQL queries Paid Members Public
Learn how to obfuscate strings in KQL queries in Azure Data Explorer. This way, the query log will not display sensitive information when someone is reviewing executed queries.
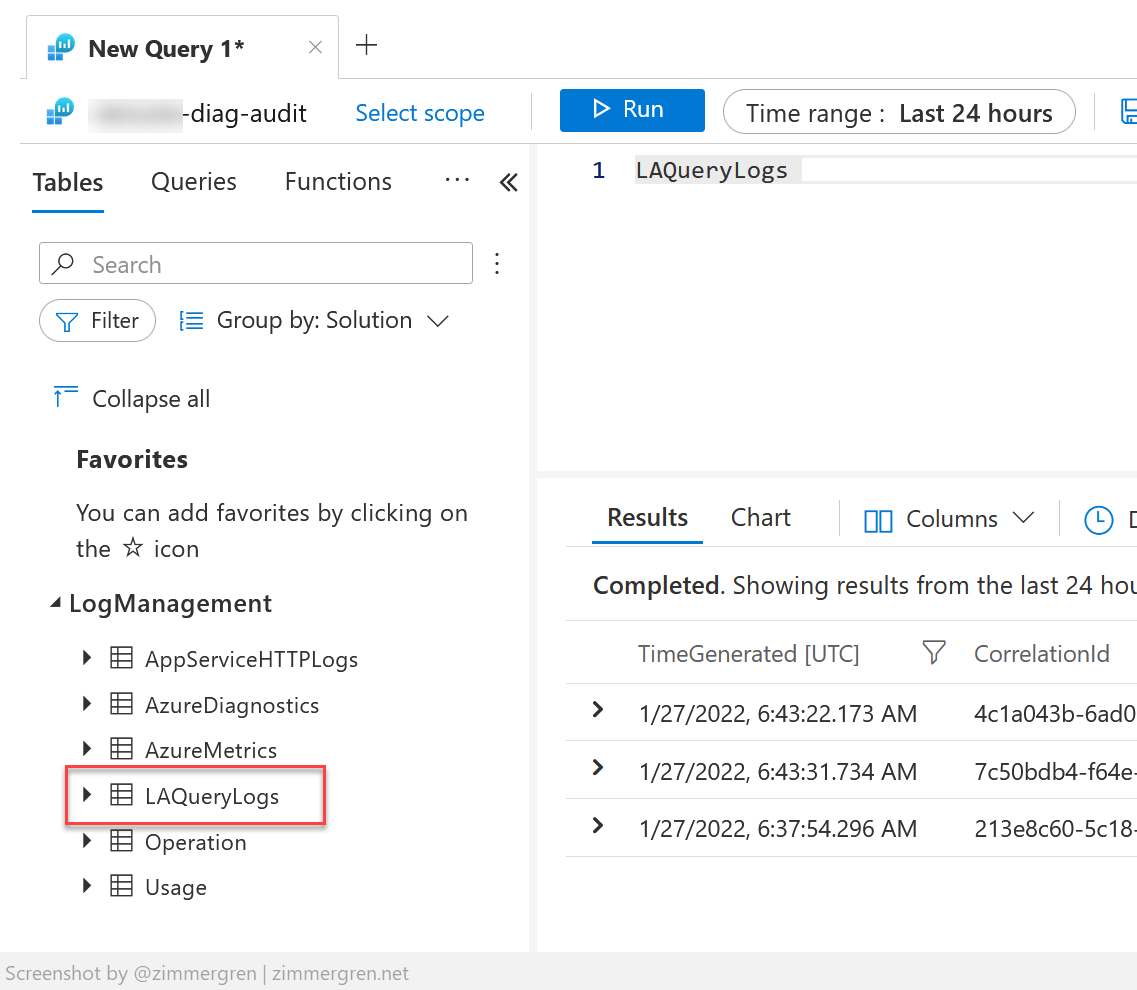
Understanding Azure Log Analytics query auditing Paid Members Public
In this post, I will talk about Azure Log Analytics and query auditing capabilities. I may cover the use cases in an article later, expanding on why this functionality matters. There are many common use cases in legislation, regulatory compliance, and monitoring, but that's for another time. Here&
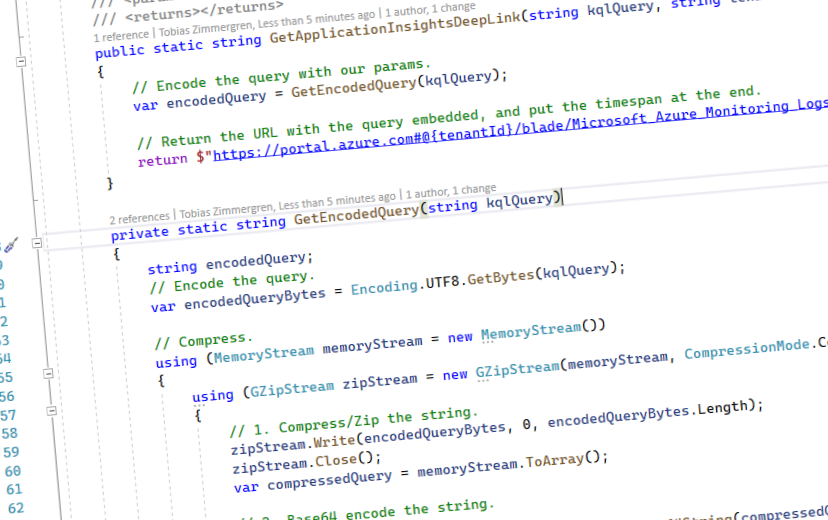
Deep-linking Azure Log Analytics and Application Insights queries Paid Members Public
For a while, I've wanted to craft deep links (direct links) to queries in Azure Monitor. Either directly to Log Analytics workspaces or to Application Insights resources I have. I have plenty of use cases for this, but most notably is the fact that we want to easily
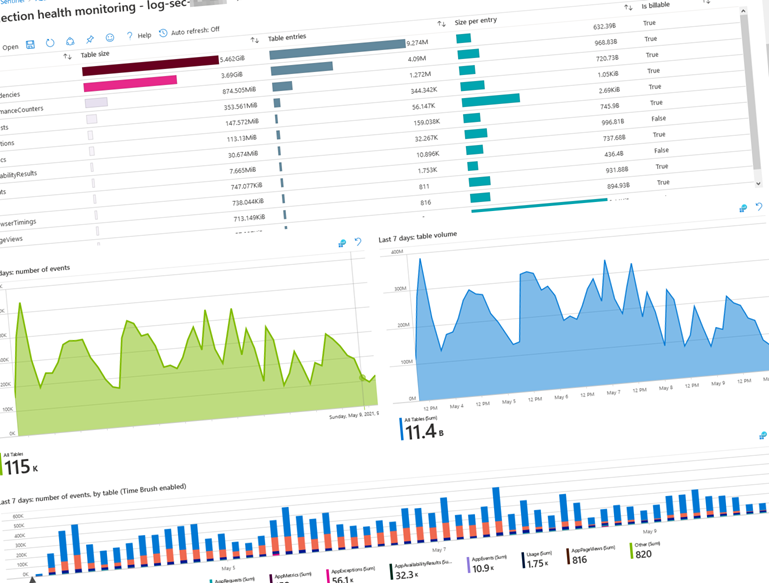
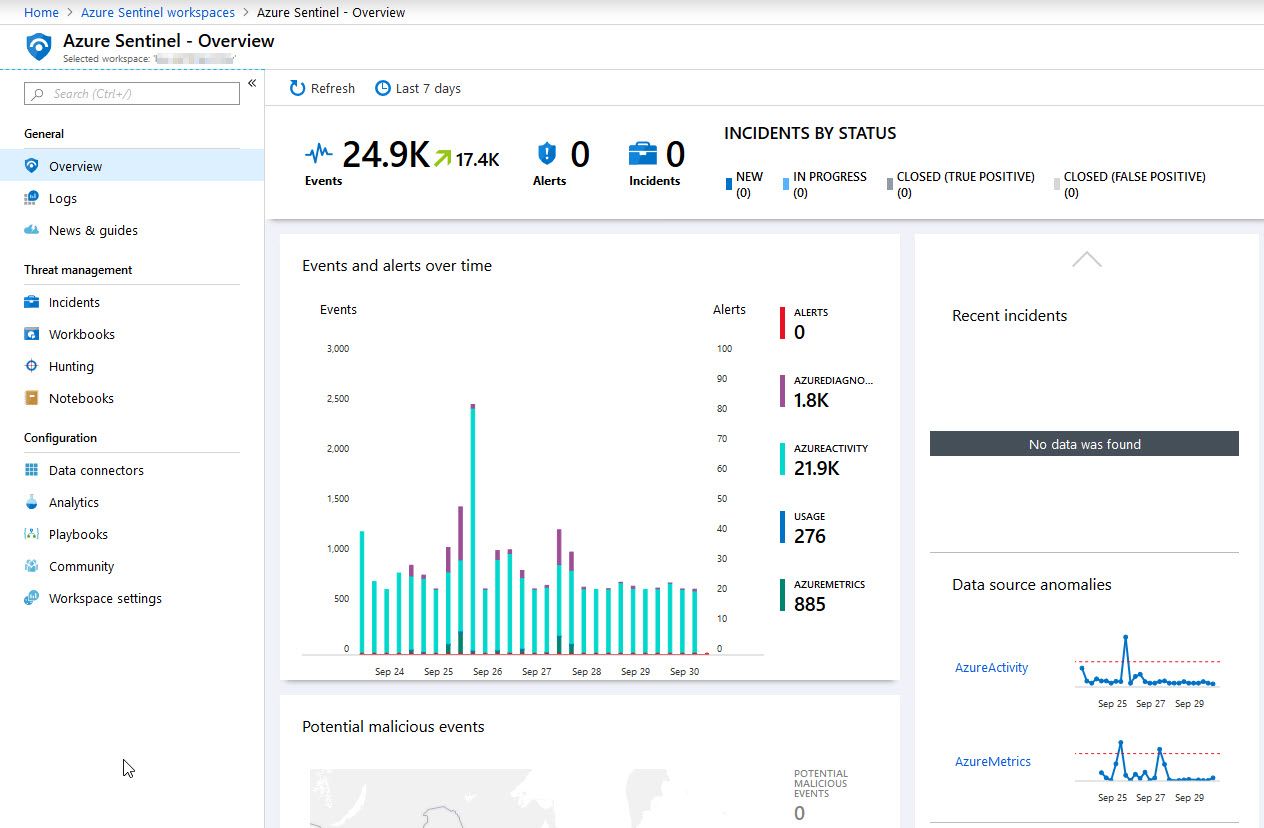
Visualize Log Analytics data ingestion using Microsoft Sentinel Paid Members Public
With Microsoft's built-in workbook template in Azure Sentinel, named "Data collection health monitoring", we can visualize the data ingestion and quickly understand our workspaces and the data we have.
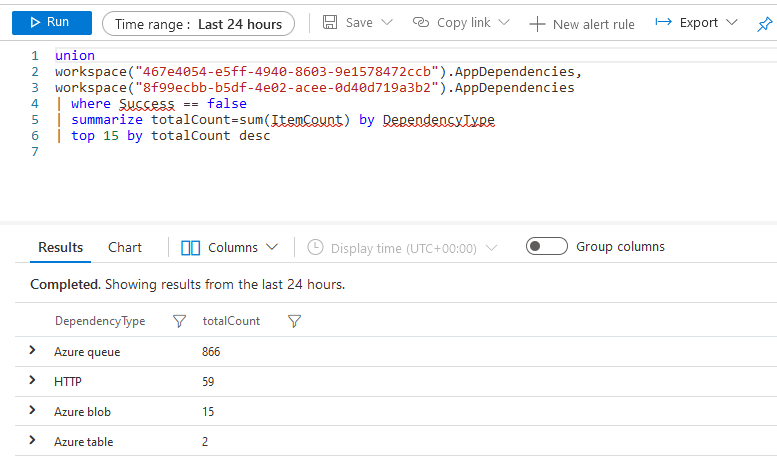
Querying data from multiple Application Insights instances Paid Members Public
Getting insights into the resources we operate is a crucial part of understanding where we need to improve and what works well. In reality, the insights and telemetry we gather exist in various regions and datacenters. Data sits in multiple subscriptions and different resource groups - even the same application
Introducing the LogAnalytics.Client NuGet for .NET Core Paid Members Public
Directly related to Log Analytics and sending entities from C#, I have previously talked about Building Custom Data Collectors for Azure Log Analytics [https://zimmergren.net/building-custom-data-collectors-for-azure-log-analytics/] and Log custom application security events in Azure Log Analytics which are ingested and used in Azure Sentinel [https://zimmergren.net/log-custom-application-security-events-log-analytics-ingested-in-azure-sentinel/] . I
Deleting Microsoft Sentinel but keep the ingested data Paid Members Public
In this post I'm sharing a tip about how you can remove the Azure Sentinel service, but keep your ingested data in Log Analytics so you can actually keep working with the data for reports and auditing reasons.
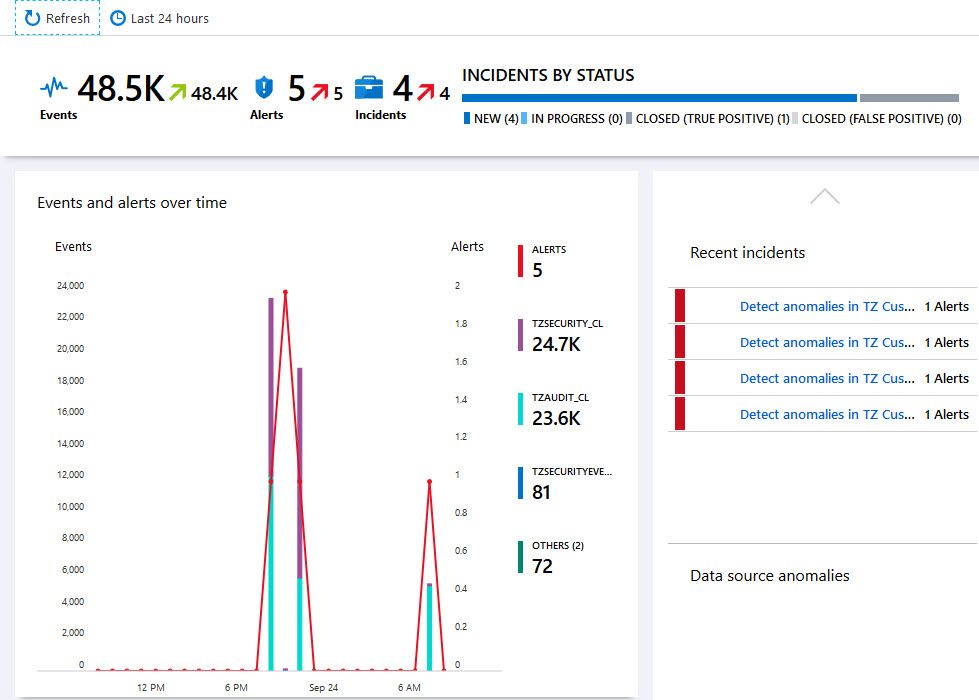
Log custom application security events in Azure Log Analytics which are ingested and used in Microsoft Sentinel Paid Members Public
A powerful capability of the Azure Sentinel [https://azure.microsoft.com/services/azure-sentinel/?WT.mc_id=ES-MVP-4021705] service is that you can ingest data from a wide variety of sources. Using Connectors [https://docs.microsoft.com/en-us/azure/sentinel/quickstart-onboard?WT.mc_id=ES-MVP-4021705#connect-data-sources] , you can even ingest data




Recent comments